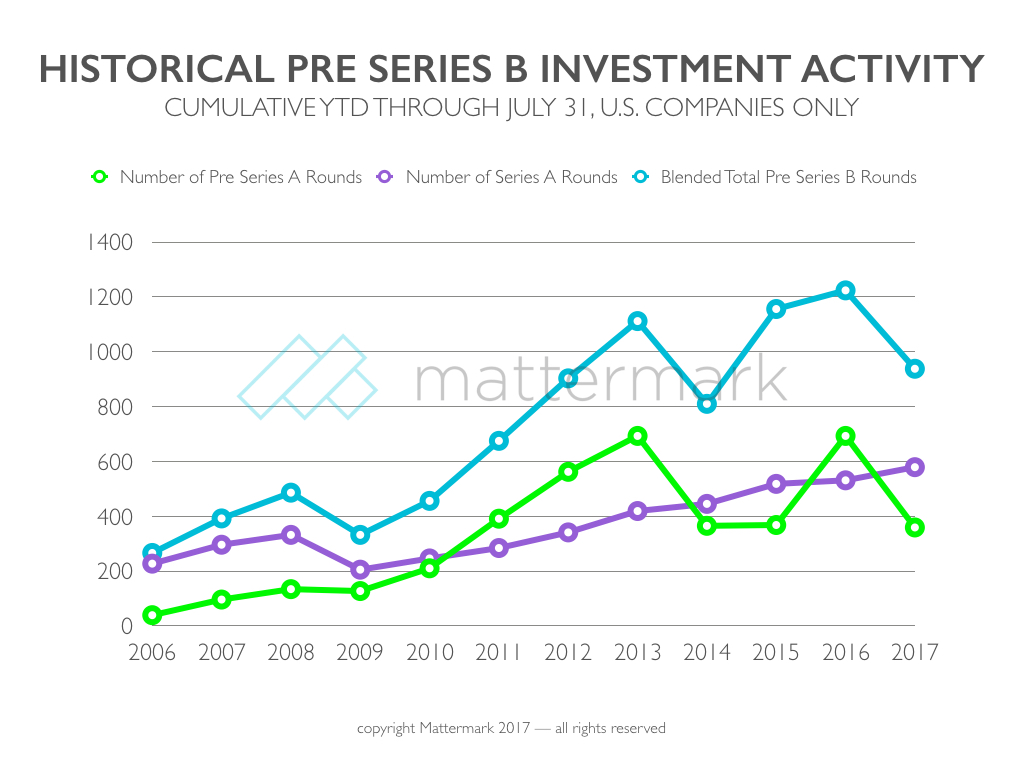
MVPs out SLC in, Startup Funding Rounds Explained, lots more – Mattermark Daily
Help People Affected By Hurricane Harvey Houston, Texas and the surrounding areas have been devastated by Hurricane Harvey. We at Mattermark urge you to donate anything you can, whether it’s… Read Full Article